Configuring Mozilla Firefox for increased privacy:
Active content, Plugins and Extensions
Table of contents:
Mozilla Firefox is a very modular browser it support active content like Java and Javascript, ActiveX, 3rd party extensions and plugins. This gives a lot of flexibility, but at the same time increases risks of losing your privacy. Here we'll cover configuration options which help to reduce this risk.
 Java and Javascript are languages fairly often used in the web
environment. The trouble with them is that they can easily be used to
obtain your personal or private data
and send it back to the website.
Java and Javascript are languages fairly often used in the web
environment. The trouble with them is that they can easily be used to
obtain your personal or private data
and send it back to the website.
Usually you can disable Java, for the most of the time, since there aren't a lot of sites that require it. Javascript is more problematic since a lot of sites use it for navigation and other things.
Obiously the safest way would be to disable both, but that will cause problems with browsing. So one of the reasonable options is to leave Javascript enabled and use NoScript extension for Firefox (available at the Mozilla plugin's site).
 Web Real-Time Communication (WebRTC) API can be used by malicious websites to make your browser leak the local IP addresses. To fix this:
Web Real-Time Communication (WebRTC) API can be used by malicious websites to make your browser leak the local IP addresses. To fix this:
 ActiveX plugins (for an example adobe flash player, windows media video (wmv) player
and others) are actually full fledged programs, they can potentially do
anything they want with your computer. There are even reports of some
Firefox extensions being used as a deployment for a trojan programs.
The safest way would be to disable all of them completely. Sadly, yet
again, this might not be an option.
So the reasonable solution is to only allow the plugins you trust and
really need.
ActiveX plugins (for an example adobe flash player, windows media video (wmv) player
and others) are actually full fledged programs, they can potentially do
anything they want with your computer. There are even reports of some
Firefox extensions being used as a deployment for a trojan programs.
The safest way would be to disable all of them completely. Sadly, yet
again, this might not be an option.
So the reasonable solution is to only allow the plugins you trust and
really need.
As a personal opinion I suggest to disable flash plugins, they might be pretty, but the problem is there were multiple exploits found in the flash player. Which would mean that in case your system is unpatched, or there is an unknown vulnerability a simple flash banner could potentially compromise your whole system.
 While the idea that browser checks site against online blacklists in-general
is good and welcome addition. The problem is that to do so
browser needs to submit the page address you are viewing to the checker's site (hopefully nothing else).
Which is counterproductive if you want extra privacy. So it's a risk vs
risk, it's up to you to choose which you want - disable suspected attack site
and suspected forgery site checks or not.
While the idea that browser checks site against online blacklists in-general
is good and welcome addition. The problem is that to do so
browser needs to submit the page address you are viewing to the checker's site (hopefully nothing else).
Which is counterproductive if you want extra privacy. So it's a risk vs
risk, it's up to you to choose which you want - disable suspected attack site
and suspected forgery site checks or not.
<< Back to Caching and Bookmarks
Mozilla Firefox is a very modular browser it support active content like Java and Javascript, ActiveX, 3rd party extensions and plugins. This gives a lot of flexibility, but at the same time increases risks of losing your privacy. Here we'll cover configuration options which help to reduce this risk.
- Java and Javascript
- WebRTC
- ActiveX and plug-ins
- Phishing checkers
- 3rd party extensions
- Conclusions and suggestions
Java and Javascript
 Java and Javascript are languages fairly often used in the web
environment. The trouble with them is that they can easily be used to
obtain your personal or private data
and send it back to the website.
Java and Javascript are languages fairly often used in the web
environment. The trouble with them is that they can easily be used to
obtain your personal or private data
and send it back to the website.Usually you can disable Java, for the most of the time, since there aren't a lot of sites that require it. Javascript is more problematic since a lot of sites use it for navigation and other things.
Obiously the safest way would be to disable both, but that will cause problems with browsing. So one of the reasonable options is to leave Javascript enabled and use NoScript extension for Firefox (available at the Mozilla plugin's site).
WebRTC
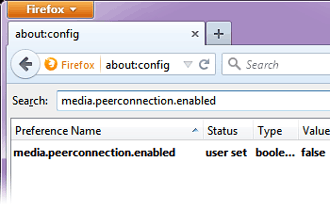
 Web Real-Time Communication (WebRTC) API can be used by malicious websites to make your browser leak the local IP addresses. To fix this:
Web Real-Time Communication (WebRTC) API can be used by malicious websites to make your browser leak the local IP addresses. To fix this:
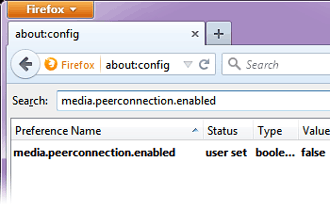
- type about:config in the address bar
- when list opens search for media.peerconnection.enabled
- set value to false
ActiveX and plug-ins
 ActiveX plugins (for an example adobe flash player, windows media video (wmv) player
and others) are actually full fledged programs, they can potentially do
anything they want with your computer. There are even reports of some
Firefox extensions being used as a deployment for a trojan programs.
The safest way would be to disable all of them completely. Sadly, yet
again, this might not be an option.
So the reasonable solution is to only allow the plugins you trust and
really need.
ActiveX plugins (for an example adobe flash player, windows media video (wmv) player
and others) are actually full fledged programs, they can potentially do
anything they want with your computer. There are even reports of some
Firefox extensions being used as a deployment for a trojan programs.
The safest way would be to disable all of them completely. Sadly, yet
again, this might not be an option.
So the reasonable solution is to only allow the plugins you trust and
really need.
As a personal opinion I suggest to disable flash plugins, they might be pretty, but the problem is there were multiple exploits found in the flash player. Which would mean that in case your system is unpatched, or there is an unknown vulnerability a simple flash banner could potentially compromise your whole system.
Phishing checkers etc.
 While the idea that browser checks site against online blacklists in-general
is good and welcome addition. The problem is that to do so
browser needs to submit the page address you are viewing to the checker's site (hopefully nothing else).
Which is counterproductive if you want extra privacy. So it's a risk vs
risk, it's up to you to choose which you want - disable suspected attack site
and suspected forgery site checks or not.
While the idea that browser checks site against online blacklists in-general
is good and welcome addition. The problem is that to do so
browser needs to submit the page address you are viewing to the checker's site (hopefully nothing else).
Which is counterproductive if you want extra privacy. So it's a risk vs
risk, it's up to you to choose which you want - disable suspected attack site
and suspected forgery site checks or not.3rd party extensions
1. Google toolbar
Lets take a look at probably the most popular toolbar. While the Google toolbar itself is fairly harmless, the problem with it is that it submits the site addresses you visit to the Google. They are supposedly using them to find new pages to index. But objectively that is a pretty large security problem. So it's better to disable it if you have it installed.2. Firefox extensions
While Firefox has a marvelous extensions out there you have keep in mind additional risks associated with their usage. Main privacy problems with addons are:- Might be storing your browsing history.
- In severe cases might be leaking it to some 3rd party.
- Installations might be purposely infected by viruses or trojan programs - consider using only signed extensions.
- Particular addons are sending information to 3rd party sites.
Conclusions and suggestions
It is possible to reconfigure Firefox in a such way it leaves fairly minimal browsing traces on the user's system. The problem with it is that a browser configured in a such way is not very user friendly. Only solution to this in, my opinion, is to use two browsers - one configured in a secure manner, other one unsecure. So then by default you use the secure one, while switching to unsecure one for sites that refuse to work otherwise.<< Back to Caching and Bookmarks
General
Anonymous Browsing - Why & How Does It Work
How to configure Firefox for increased privacy
Standard vs Pro version
Automatic Proxy Switching
Anonymous Browsing Using Socks servers
How to force program to use proxy server
Use Case - Anonymous Torrents
Use Case - Dealing with Group Policy proxy settings
Use Case - beating BBC iPlayer
Use Case - beating Hulu.com
Use Case - beating Forum IP ban
Use Case - beating Rapidshare.com
Use Case - watching YouTube.com's not available videos
Use Case - posting on Craigslist
Proxy Scanner Options Explained
Special GEO Handling
In-Depth Proxy Server Testing
Proxy Test Target Management
Import/Export proxy lists
Internal Proxy Servers
PlayStation 3 + Proxy Switcher
ProxySwitcher's proxy scanner: Maximizing Scanning Speed